電腦安全-L22
Secure E-mail
MIME
- 一種
網路郵件格式:對 RFC 822 規範的擴展- RFC 822: Defines a simple heading with To, From, Subject
- Assumes ASCII text format
- 提供新的標頭欄位: 定義
郵件內容的資訊
S/MIME
- 安全/多用途網際網路郵件擴展 (Secure/Multipurpose Internet Mail Extension)
- 對 MIME 郵件格式的
安全增強- Based on technology from
RSAData Security
- Based on technology from
- 提供對電子郵件進行
簽名和加密的功能 - 比較
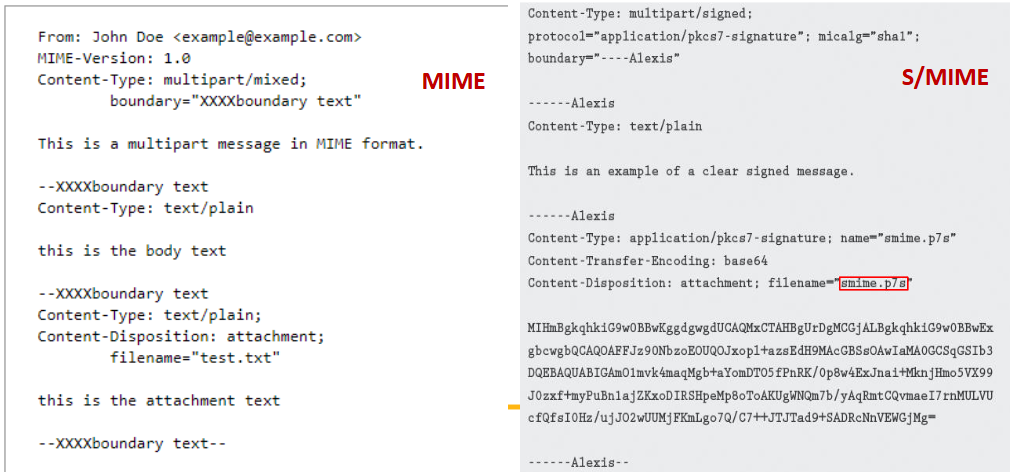
- 加密流程
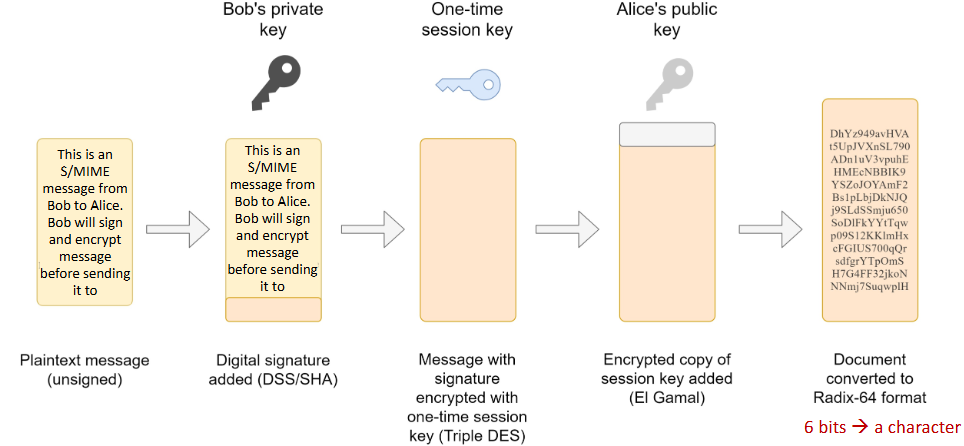
- S/MIME Functions
Enveloped data- 加密的內容以及相關的金鑰 (用收件人的公鑰加密)
- 預設演算法是 AES 和 RSA
- M → AES(M) →
AES(M) + RSA(K)- M: 郵件內容 (Message)
- K: 隨機生成的對稱密鑰 (pseudorandom secret key)
- 使用收件人的公鑰進行 RSA 來加密 K
Public-key certificate: 讓 S/MIME 廣泛使用
Signed data- Base64(content + sig)
- 訊息和簽名摘要
一起編碼
Clear-signed data- content + Base64(sig)
- 明文訊息 +
編碼的簽名摘要
Signed and enveloped data- 簽名和加密資料的巢狀結構
DomainKeys Identified Mail
DKIM
- A specification of
cryptographically signing e-mail messages- 由 signing domain (發信網域) 對郵件負責
- 已被多數電子郵件服務廣泛採用
- ex: gmail, yahoo, and many ISPs
- 使用原因:
- S/MIME 需要
寄件者與收件者都使用 S/MIME - S/MIME 只簽署郵件內容,
Header資訊可能被竄改 - 對使用者
透明(Transparent),使用者不需要任何動作 - 適用於合作網域的所有郵件
- 防止攻擊者偽裝成合法寄件者
- S/MIME 需要
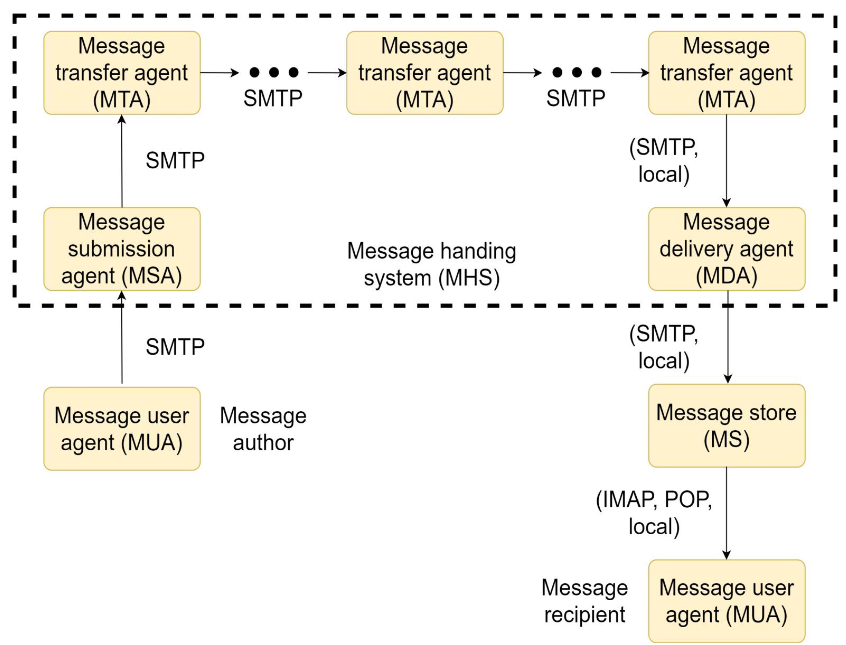
- Internet Mail Architecture:
- User world: MUA
- Transfer world: MHS (Composed of MTAs)
- MSA: Signer
- MDA: Verifier
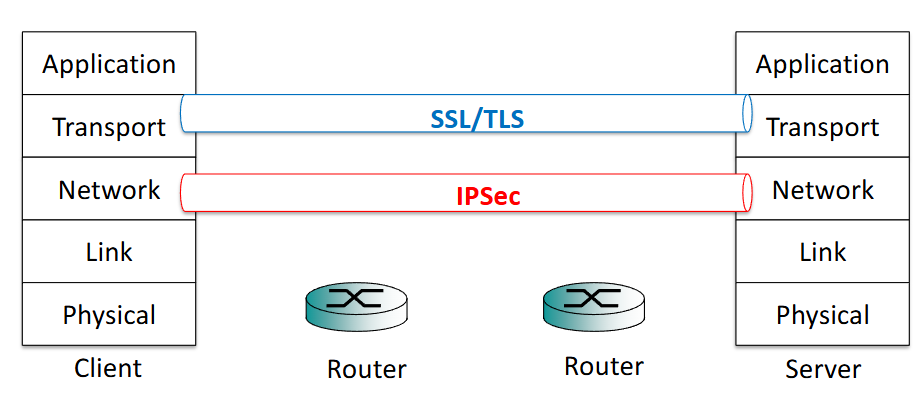
SSL and TLS
- Secure Socket Layer (SSL)
- 使用最廣泛的安全服務之一
- SSL3.0, SSL2.0 (deprecated in 2015)
- Transport Layer Security (TLS)
- General-purpose service: 是一組建立在 TCP 上的協定
- TLS1.3, TLS1.2, TLS1.1 (new standards)
- 實作方式:
- 作為底層協定的一部分: 對應用透明
- 嵌入在特定應用中,ex: 瀏覽器內建 SSL
- SSL/TLS Protocol Stack
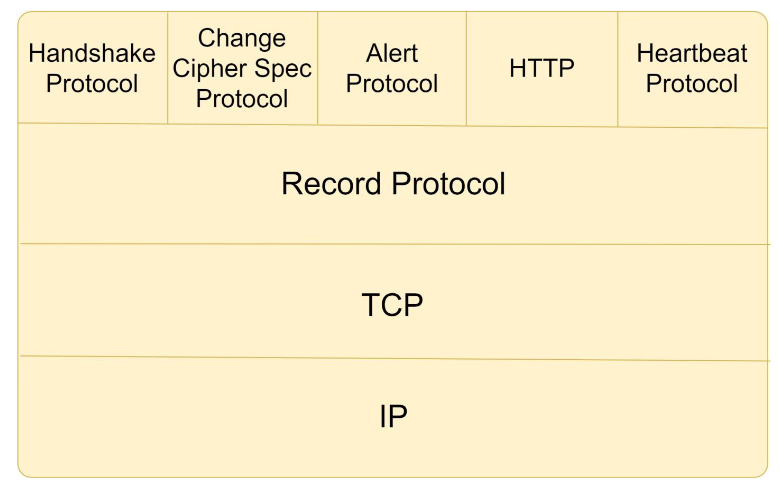
- TLS Concepts
- TLS Connection
- 屬於傳輸層 (
transportlayer) 的連線 peer-to-peer(點對點)transient(暫時的)- 每個 connection 都會
對應到一個 session
- 屬於傳輸層 (
- TLS Session
- An association between a client and a server
- 由
handshake protocol 建立 - 定義一組加密安全參數
避免每次 connection 都重新做昂貴的協商
- TLS Connection
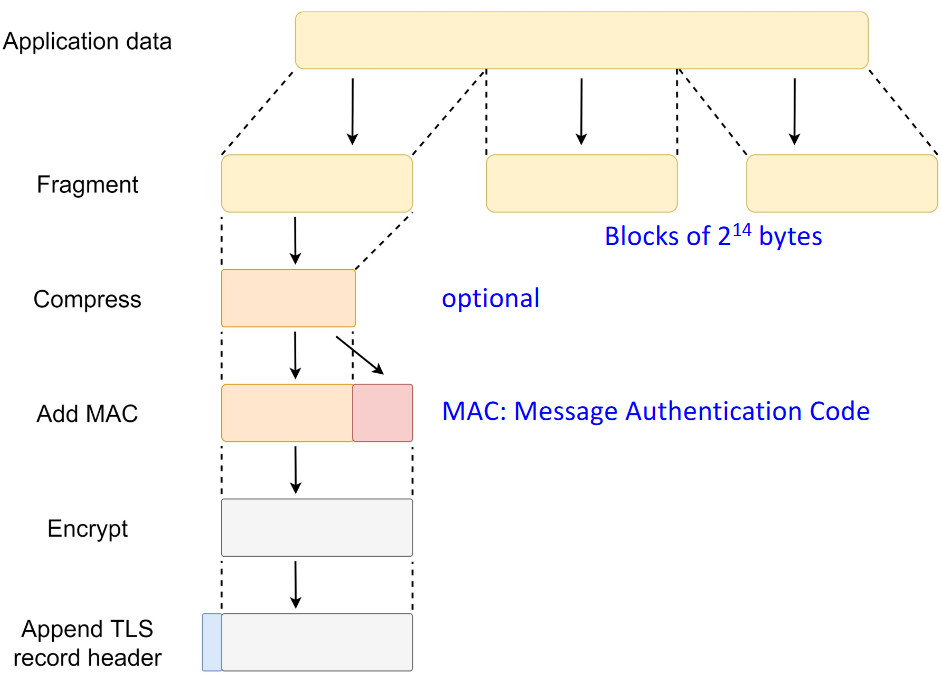
Record Protocol
- Two services
Confidentiality- Message
integrity
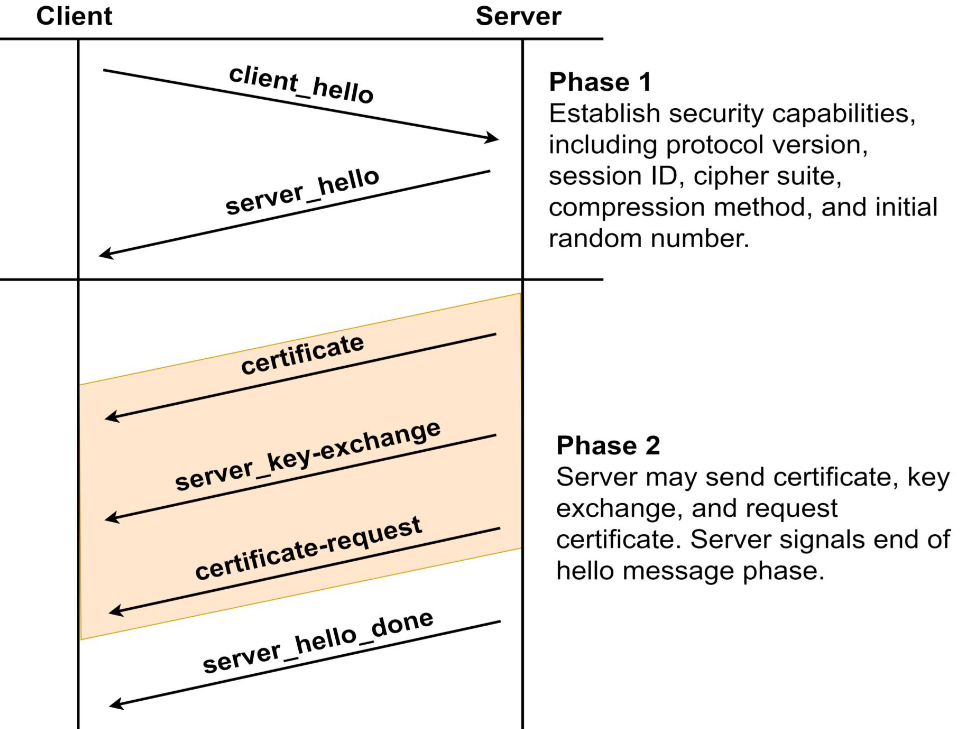
Handshake Protocol
- Most complex part of TLS
- Used
before any application data are transmitted - Allows server and client to:
Authenticateeach other- Negotiate
encryption and MAC algorithms - Negotiate
cryptographic keysto be used
- Comprises a series of messages exchanged by client and server
- Exchange has four phases
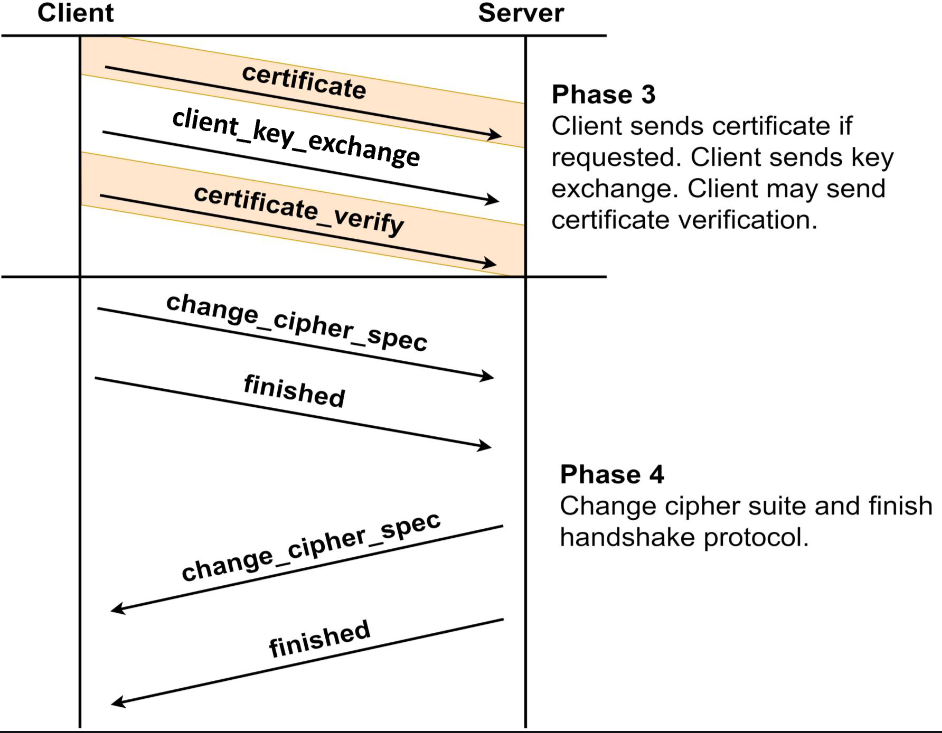
Change Cipher Spec Protocol
- One of four TLS specific protocols that use the TLS Record Protocol
- the simplest
- Consists of a single message:
- a
single bytewith thevalue 1
- a
- 目的: 將
pending state複製到current state- 更新目前使用的加密參數 (cipher suite)
Alert Protocol
- Two bytes
- First byte: warning (1), fatal (2)
- 若為 fatal,TLS 會立即終止該 TLS connection
- Second byte: specific alert code (RFC5246-appendix)
- First byte: warning (1), fatal (2)
Heartbeat Protocol
- 由硬體或軟體定期產生的訊號
- 用來表示系統正常運作,或用來同步系統各部分
- 來監控某個協定實體是否仍然可用
- 目的:
- 向寄件者保證收件者還活著
- 避免 connection 因閒置被關閉
Major Improvements in TLS 1.3
- Performance boost
Fewer round trips(1-RTT) reduces latency- Faster session resumption using 0-RTT
- Stronger security
Deprecated weak algorithms(RSA key exchange, SHA-1, CBC)- Perfect Forward Secrecy (PFS) is mandatory, improving long-term security
Fully encrypted handshake protects metadata
- Simplified protocol
- Fewer cipher suites =
reduced attack surfaceand easier management
- Fewer cipher suites =
SSL/TLS Attacks
- Attacks on the Handshake Protocol
- Attacks on the record and application data protocols
- Attacks on the PKI
- Other attacks
HTTPS (HTTP over SSL)
- Combination of
HTTPandSSL
IPSec
Applications of IPSec
- 建立分公司之間的安全連線
- 遠端存取
- 與合作夥伴建立外部網路 (Extranet) 或內部網路 (Intranet) 連線
- 提升電子商務的安全性
Benefits of IPSec
- 對所有流量提供強安全性
- all traffic at a firewall or router
- 防止繞過防火牆
- 對應用程式透明
- 對使用者透明
- 防止攻擊者破壞通訊或截取部分流量
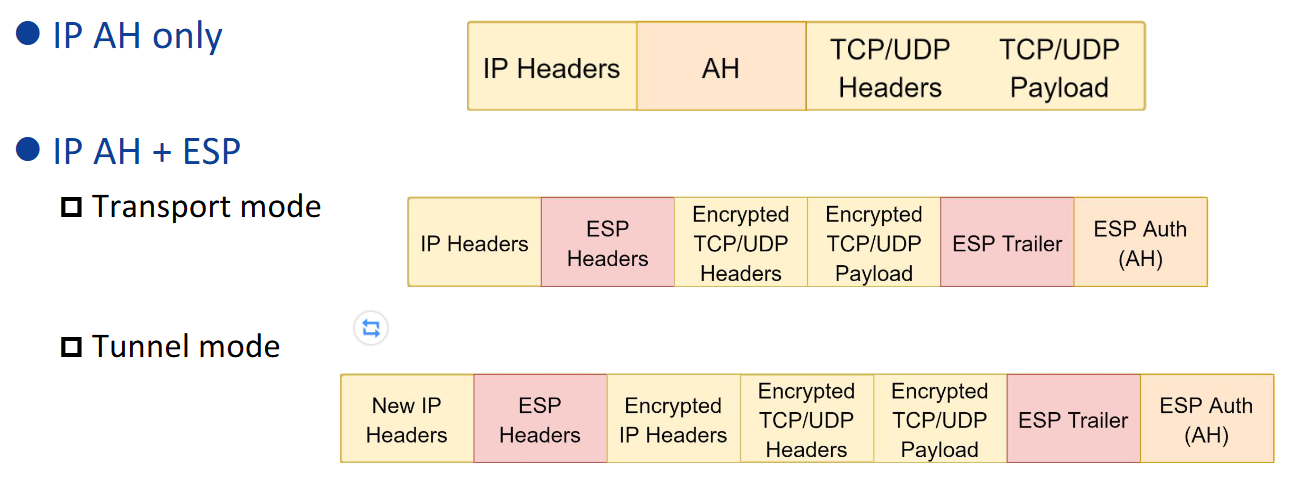
The Scope of IPSec
- Two main functions
- Encapsulating Security Payload (
ESP):- A combined
authentication/encryptionfunction
- A combined
- A
key exchange function:- Internet Key Exchange standard (IKEv2)
- Encapsulating Security Payload (
- VPN: 需要 authentication and encryption 功能
- Authentication Header (AH): authentication-only function (deprecated)
Security Associations
- IPSec 是
One-way關係: between a sender and a receiver - Two-way secure exchange: 需要兩個 SA
- Uniquely identified by three parameters
- Security parameter index (SPI)
- IP destination address
- Protocol identifier: AH or ESP
Two IPSec Operation Modes
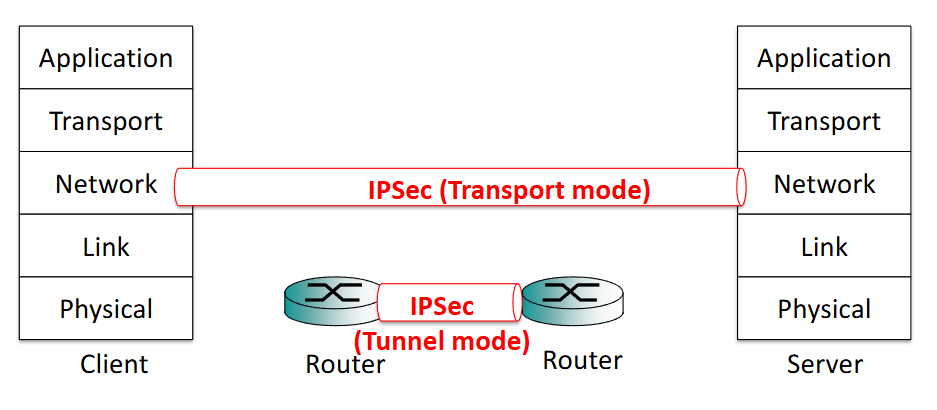
Transport Mode
- 保護: IP 封包的 payload
- 用途: 兩台主機之間的端對端通訊
- ESP 保護 IP payload 而不是 IP header
Tunnel Mode
- 保護: 整個 IP 封包
- 用途: SA 一端或兩端皆為安全閘道 (security gateway)